More and more employees find it easier to use a single cloud for private and business purposes instead of organizing different clouds which can be very time-consuming. The lines between the private and business use of mobile devices have become blurred and are not clearly separated.
But why could this be an issue? Let us take a closer look at the phenomenon called BYOD (“Bring Your Own Device”).
Over the last decade we can say with all certainty that technology has made a great impact on numerous individuals and makes life easier in many different aspects. Smartphones and tablets are great communication tools which make it easier to keep in touch with our loved ones and co-workers. We can check our emails at the barber shop, organize and plan business trips within a few minutes and buy a last minute gift for grandma’s 86th birthday party at the Italian restaurant next door. Mobile devices offer a variety of useful tools many people do not want to miss in their daily lives anymore.
This is one of the reasons why many employees also use their private devices, like smartphones and tablets, for business purposes, since they want to increase their efficiency as well as their productivity. But what sounds good at first glance can in fact create a series of complications if not used carefully.
Why people carry two phones
There are two main problems with BYOD: The problem for the company is safety. It is way harder for the employer to control the appropriate use of personal devices with sensitive company data on it. When workers have this data on their phones, they automatically become a potential source of danger since the safety of the private device can’t be guaranteed. While company provided smartphones are usually mandatory passcode protected with the need to change such passcode frequently paired with a short lock time – and no such settings can be altered, losing a private phone when having work-related files on it can lead to career ending consequences for the employee and serious damages for the company.
The problem for the employee is privacy when using your own device at work. Some workers might fear that the employer will have access to private pictures, messages and their personal data in general since the same networks and clouds are used for personal and work-related data.
For these two reasons common practice is to carry two phones. However this is not the solution! And I’m not just talking about that it is a waste of money and resources to stay up-to-date with two devices in today’s race of software updates and newest hardware, but way more interesting is that the above mentioned problems are not at all addressed: The reality is that there are times when the employee does not want to carry two devices but still wants to be connected to his job – e.g. when going out at night. Then what happens is that company data will be forwarded to the private device – which becomes a danger to the company at a time when the device is most vulnerable to theft or loss. And this is true for all companies who do not have a BYOD policy or do not provide a company smart phone. The smarter companies restrict company data to company devices only, however this restricts the flexibility of the employee and ultimately leads to productivity loss. If only Blackberry phones are allowed and you have an iPhone advocate – the user won’t happily and efficiently use the company device but rather voice his concerns about his company’s inefficiency.
Employees and companies should also be aware of the fact that BYOD has certain limitations. Different types of mobile devices (iPhone, Blackberry, Samsung…) have different operating systems and there is usually no standardization possible. It is not easy to ensure that every employee has exactly the tools he or she needs for work and it can be quite risky to use networks without appropriate firewalls.
In summary no BYOD policy will ultimately put the company at risk and a too restrictive policy will limit the employees output. This means the companies need to act now!
The ideal BYOD solution
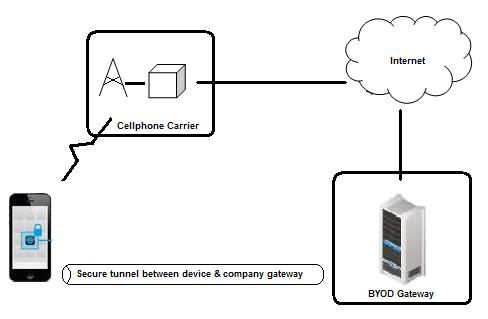
The solution is that employees are allowed to use their own devices under certain circumstances. Companies should ensure that there is a possibility of switching between the personal and work environment. Providing a secure corporate app which in essence is a section on the BYOD used for work would be such an option. This makes it easier to protect and monitor the work relevant data used by the employees. This secure container is not accessible by any unauthorized person and allows the internal IT of the company to simply delete it if the employee loses his device or leaves the company. Personal data and personal apps are not affected and not accessible for the employer. The implementation of MDM (Mobile Device Management) software is therefore highly recommended to optimize the security of the corporate network. It gives the company the ability to control and protect the data and reduce business risks at the same time.
A secure container (or: sandbox) can not only protect from viruses, but also encrypt the data and delete it from remote, if necessary. The solution can be installed locally or in a private cloud and provides advanced data protection features without limiting the productivity of users. The security mechanism separates running programs and isolates protected applications so they cannot be touched by outside influences or interact with other applications. PASS itself provides a BYOD/Sandboxing solution (PASS Connect) in cooperation with Good Technology, as well as Mobile Device Management in cooperation with Sophos.
Next week let’s talk about BYOD in the travel industry…
Image by violetkaipa