Today I want to speak about the danger of mobile devices (incl. BYOD) when you travel.
Not only employees, but also leisure travelers use mobile devices and rely on public networks including hotel-, airport- and onboard Wi-Fi. The possibilities are endless and yet many airlines are not aware of the great potential BYOD can provide for them. As we already know, especially business travelers tend to use their own devices during a trip. Offering them free (or inexpensive) Wi-Fi gives them the possibility to work on projects, check their emails or get updates on delays and bookings, all while still being on board. This can not only improve the customer loyalty, but also lead to a better work/life balance of the passenger, employee and BYOD user.
BYOD – Above the clouds
An option is the on-board entertainment via BYOD: It allows travelers to use their own devices during the flight and choose from a variety of movies, TV, songs and radio programs. This kind of entertainment allows the passengers to use their own gadgets which they feel comfortable with instead of slow and aging seat-back video screens. The passengers do also get access to a moving map and live flight information; all they need to do is download the app in advance.
This kind of BYOD service can not only improve the onboard passenger experience but also save the airline a large amount of money by not having to spend it for expensive in-flight entertainment systems and its upkeep. No additional weight for the displays does also mean that the airplanes are getting lighter and burning less fuel, the end result being that airlines can keep the fare at a reasonable price.
Even the cabin crew can benefit from the BYOD trend. Using their own devices can increase their efficiency as well as the customer satisfaction. The crew could not only get access to digital passenger lists, but also to specific meal reservations and important medical information. This way a more personalized service can be offered to the travelers which, in return, can build a better brand loyalty and revolutionize the travel industry on many different levels.
Another interesting topic in the context of personalized services through the passengers own mobile devices is iBeacon, which is built into iOS 7. It is a wireless Bluetooth technology, which provides location-based information and services to their users via push notifications. Beacons are small Bluetooth transmitters which can provide you with information if you have the app of e.g. a shop with beacons installed on your device. Virgin Atlantic has started using iBeacon at the London Heathrow airport in 2013. Passengers at the security checkpoint don’t need to stressfully fish their boarding passes out of their huge bags anymore; they automatically appear on their smartphones, ready for inspection. This small and simple feature allows airlines to provide their passengers with a lot of useful information, for example indoor directions or walk times to gates.
Do not put your company data at risk
However many people are not aware of the security vulnerabilities of accessing any public wireless network from their device (not to mention personalized location services provided by iBeacon). The signals provided are usually not secure and not as well monitored as signals provided by cellphone carrier and anyone who uses the same hotspot can intercept sensitive personal and corporate information. The missing security net at the airport and on airplanes is a risk and not any safer than the Wi-Fi network at your favorite coffee shop or mall. Airplane and airport hotspots are usually only secure while you give them your credit card information and purchase time on the wireless network. After that, no encrypted connection can be provided and it is easy for hackers to get the passengers sensitive data without them even knowing it.
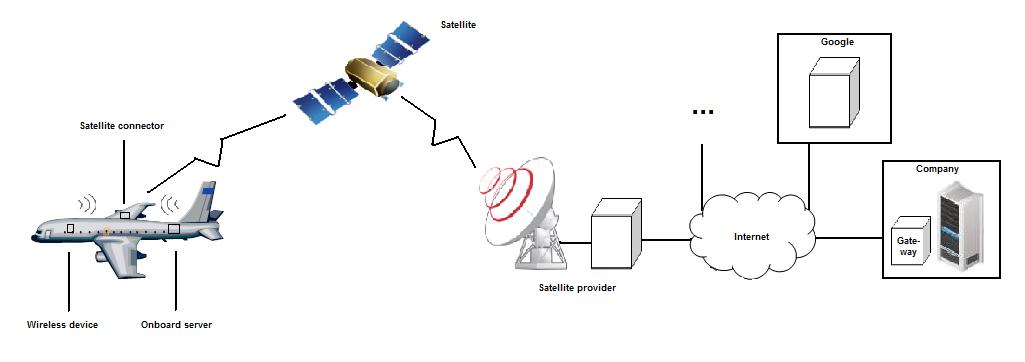
While the hotspots are usually connected via a fiber optic landline with high bandwidth or similar to internet, on an airplane the connection is done via satellite. However a bidirectional satellite connection of a moving target (airplane) is not easy, does not come with a large bandwidth and is costly. This is why such systems generally employ caches where frequently used internet pages are stored locally on the server in this case on the airplane. So if 20 people on the same aircraft check the latest football score only one time the aircraft needs to get this information through the satellite connection (until the score changes again – of course). Have you ever seen a popup on your favorite browser that the server certificate of Google could not be verified? This is exactly the case when the Google page is opened from a cache and not from a ‘real’ Google server.
So because of these reasons, mobile devices – especially BYOD – are even more vulnerable in the air than on the ground and employer sensitive data is not even close to being as secure as within the corporate wireless environment or wired environment within your own premises. Another reason why companies need to address the issue that every possible device which can contain company sensitive data needs to be secured, especially in light of BYOD.
Business travelers who have their company’s confidential business information on their laptop usually set up a VPN (virtual private network), a tunnel between the device and the company gateway which encrypts all communication between the two access points. It is a helpful tool for protecting online privacy and employees can use it to access files and other resources, all while being securely connected to a remote network via Wi-Fi. Similar protective measurements need to be taken for other mobile devices as I already mentioned in my previous blog. It had to be mentioned though that vulnerability in regards to viruses and Trojan horses are also higher on these public networks and employee education about the risks is also an important step towards security of company sensitive data.
Image via Shutterstock